Choosing the Right Security Services Provider
Managed Security Services – the Next Frontier
Several weeks ago we wrote a blog post titled, “A Look at 2023’s Top 5 Cyber Risks – and Strategies for Defending Against Them;” we discussed the following Cyber Risk issues:
Strategy 1: Build Your Resistance to RaaS
Strategy 2: Don’t Blame Your Employees — Give Them Better Training
Strategy 3: The AI Arms Race – Prepare for Battle
Strategy 4: Look After Your Cyber-Talent
Strategy 5: Review the Merits of Cyber Insurance
Prior to that blog post we wrote another titled, “Top 5 Cybersecurity Trends to Watch in 2023,” we discussed the following Cyber trending issues:
Strategy 1: Build Your Resistance to RaaS
Strategy 2: Don’t Blame Your Employees — Give Them Better Training
Strategy 3: The AI Arms Race – Prepare for Battle
Strategy 4: Look After Your Cyber-Talent
Strategy 5: Review the Merits of Cyber insurance
Further, we said, “according to Gartner, organizations will spend a collective $188.3 billion on information security and risk management products and services in 2023 on three transitionary megatrends: remote work, zero trust network access, and the cloud.”
In this blog post we’ll discuss the evolution of the security services business and how you can choose the most appropriate solution for your organization. Let’s get started…
As business leaders operationalize their strategies for 2023, cybersecurity is high on the boardroom agenda for many reasons – on the top of the list is obviously the number of successful attacks has skyrocketed and the results have been devastating for nearly countless organizations. Let’s take a moment to look at the evolution and impact of cybercrime over the last year.
A report published by Cybersecurity Ventures asserts that the global cost of cybercrime exceeded $7 trillion in 2022. We all know that the impact of a successful cybersecurity attack – damage to brand reputation, trust, and profitability of the business – can take years to recover from.
It’s not surprising that the fight against cybercrime is attracting board-level interest. The latest figures from Gartner indicate that security and risk management will rise to the top of the list of technology priorities for medium-sized enterprises in 2023. As a matter of fact, globally, the number of enterprise-level cyber-attacks has risen exponentially in the past year:
- During the first half of 2022, there were a total of 236.1 million ransomware attacks worldwide.
- In September 2022 alone, cybercriminals successfully gained access to and compromised 35 million files, targeting businesses’ sensitive or confidential information.
- The global cost of cybercrime is predicted to reach $11.5 trillion in 2023.
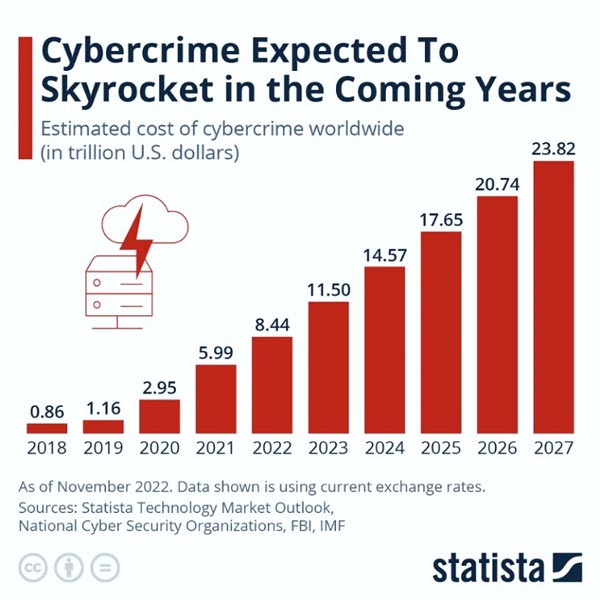
Figure 1: The Real Cost of Cybercrime
Source: https://www.statista.com/chart/28878/expected-cost-of-cybercrime-until-2027/
Attacker techniques are becoming more advanced. Increasing numbers of sophisticated tools are available on the Dark Web to enable scammers. And as more people conduct their personal and business affairs online, the attack surface continues to expand.
Many businesses are incorporating outsourced security services into their enterprise risk strategy to bolster their cyber-defenses.
This blog post will explore the evolution of the security services market and the key players, specifically focusing on managed security services providers (MSSPs). We’ll also consider what to look for in an MSSP partner if you’re considering going down this route.
Understanding the Security Provider Ecosystem
The information security marketplace is a complex one and the term “security provider” covers a variety of entities that offer security products and services. Let’s break it down:
Resellers
As the name suggests, these players resell security vendors’ tools, typically endpoint detection, anti-virus, or firewall products. Most resellers have close relationships with particular vendors and typically recommend their products to their customers.
While some resellers offer an additional, basic layer of product support, it’s important to note that their services don’t include ongoing threat monitoring or advanced security advisory services.
Penetration Testing Service Providers
Companies engage penetration testing service providers to undertake ethical cybersecurity assessments to identify and attempt to exploit any vulnerabilities existing in their networks, systems, applications, and websites. The company can then use the information gathered to address discovered weaknesses and mitigate the risk of suffering a malicious attack.
While penetration testing provides value, in isolation, it’s insufficient to build a comprehensive enterprise security posture.
Managed Detection and Response Providers (MDRs)
MDRs use both technology and human expertise to perform threat-hunting, monitoring, and response activities. MDR services allow companies to quickly identify and limit the impact of threats.
However, MDRs don’t generally include managing firewalls and the other day-to-day network security needs of an organization in their scope of work. These tasks are more suited to internal network managers or an MSSP that can offer a more specialized service. (More on MSSPs a little later.)
Managed Service Providers (MSPs)
MSPs focus on managing an organization’s IT needs on its behalf. While they have specialized knowledge of managing complex, multi-technology environments, they haven’t traditionally focused on their customers’ security requirements.
However, in the last few years, many MSPs have sought to extend their expertise into the security space so they can meet the increasing demand for these services and grow their margins.
Managed Security Service Providers (MSSPs)
MSSPs focus exclusively on security. They don’t offer IT services, nor do they position themselves to customers as a technology “one-stop shop. They perform threat research, constantly scan their customers’ environments for threats, write bespoke threat detection logic, and perform penetration testing and detection, defense, and incident response activities. MSSPs employ people with domain-specific security expertise, such as security architects, engineers, and analysts.
The MSSP market is projected to have a compound annual growth rate of 14–16% through 2031, compared to an estimated 10% for the MSP market.
Which Outsourced Security Option is Best for You?
When it comes to protecting your business from the scourge of cybercrime and other devastating data loss events, it’s clear that you have an array of options. Factors influencing your decision will include the size of your organization, the industry in which you operate, your budget, your level of in-house expertise, and your appetite for risk.
Let’s consider several scenarios:
Some organizations are simply unaware of the importance of cybersecurity. Others haven’t experienced any issues, so just assume that all is well. Many such companies never implement any security measures beyond a basic anti-virus and/or just employ a generalist IT technician. Unfortunately, many of those that adopt this “let’s keep our fingers crossed” approach live to regret it.
Many businesses set out to build an in-house team. However, this effort can hit a roadblock if there’s a lack of buy-in from the top or budgetary constraints. What’s more, qualified security talent is both scarce and expensive. Research shows that talent management was both the #1 priority and the top obstacle facing security leaders in 2022.
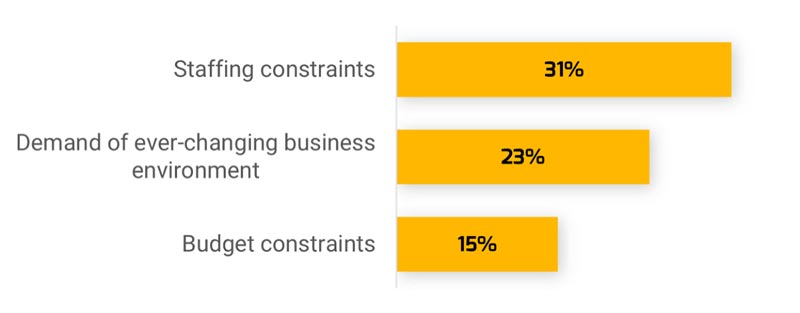
Figure 2: Staffing Constraints Top the List of Security Leaders’ Challenges
Source: https://www.infotech.com/research/ss/security-priorities-2022
Some organizations that are unwilling or unable to hire a dedicated security team or engage with a dedicated security partner decide to purchase security tools – either independently from a vendor or through a reseller. This approach also comes with a downside. Without the knowledge and skills required to select the right products and maximize their effectiveness, your enterprise security defenses will be porous.
That’s because to keep your organization safe, you also need advanced insights regarding:
- What threats are unique to your organization
- How to get complete visibility into what’s happening in your environment
- How to detect threats and potentially malicious behavior
- How to respond rapidly yet efficiently
All this is driving up the demand for MSSP services. The global managed security services market is expected to generate revenue of $53.2 billion by 2031, a 264% growth from 2021’s figure of $14.6 billion.
Enlisting an MSSP partner can be an excellent option for companies that have an in-house IT team but recognize they need advanced levels of technical security expertise.
Where to Next? The Future of Managed Security Services
The current dynamics within the MSSP marketplace make for an interesting study. Some of the key forces in play include increased competition, industry consolidation, and growing M&A activity:
- We expect to see a trend whereby more MSSPs will be acquired by larger MSSPs seeking to entrench their position as leaders in the market, establish a presence in new geographies, and tap into diversified talent pools.
- Likewise, as we touched on earlier, certain established MSPs will look for opportunities to buy MSSPs.
- More cyber-insurance providers will explore the MSSP acquisition path.
What to Look for in an MSSP
If you’re considering engaging an MSSP, be sure that your shortlisted candidates can bring the following to the table:
- Proprietary security tools and methodologies that can deliver end-to-end monitoring, protection, detection, and incident response and remediation capabilities.
- Advanced threat intelligence advisory, threat hunting, customized detection content, and attack simulations.
- A qualified team of security architects, engineers, technicians, analysts, and specialists who are certified in multiple areas of enterprise security.
- Experience with securing endpoint devices using a variety of software and hardware frameworks.
- A professional services arm that can be contracted to regularly perform functions that your security organization doesn’t have the knowledge or the time to fulfill.
- A specialized helpdesk providing support for security-related software.
Conclusion – A High Stakes World Demands High-end Security
When it comes to enterprise security, the stakes are high, and the time to act is now.
As we move through 2023, more enterprises will acknowledge the wisdom of enlisting MSSPs to access advanced levels of security protection at an affordable cost.
It’s the responsible move for companies seeking to access the right people, processes, and technologies; protect their market reputation and leadership position; and give information- and cybersecurity the attention it rightfully deserves.







