Developing a Risk-Based Vulnerability Management Program A Real-Life Case Study
Custom Security Solutions Empower Organizations to Create Robust, Efficient Vulnerability Management Programs Vulnerability management exists for the purpose of identifying and remediating vulnerabilities in systems quickly before they are exploited. Vulnerabilities,
The SolarWinds Sunburst Attack: How to Protect Yourself from 5th Generation Cyberattacks
Last week US government offices were targeted by one of the most sophisticated and severe attacks seen in history both because of the sophistication and scope. A series of mega
Bug Bounty Programs are Becoming Increasingly Effective
What is the Difference Between Bug Bounty and Vulnerability Management Programs? In this blog, SecureOps Senior Penetration Tester Jasmin Landry has provided us deep insight into bug bounty programs in two
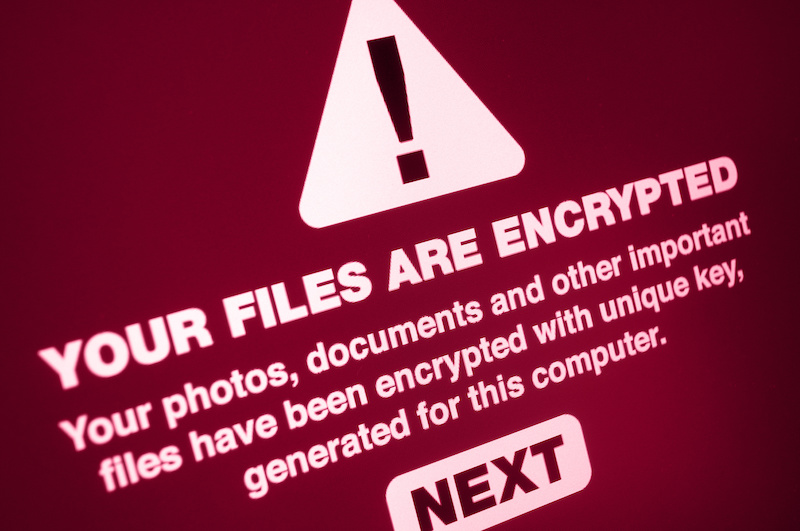
Why MAZE Ransomware Attacks are So Devastating
Why MAZE Ransomware Attacks are So Devastating MAZE ransomware is quickly becoming one of the most devastating strains of Windows ransomware that have infiltrated companies and organizations around the world and
4 Key Steps to Stopping Ransomware Attacks
How Significant is the Ransomware Problem? In writing this blog post we reviewed data from a variety of surveys including the Verizon Data Breach Report, the Cybersecurity Insiders Survey, the Ponemon