2020 Top 5 Cyber Security Predictions
Top 5 Cyber Security Predictions for 2020
In conversations with industry analysts, our customers, combing through the statistics like Comparitech’s breach data and ultimately talking amongst ourselves we came up with 5 IT security predictions for 2020 that may not be surprising, however, they are very likely. Our goal in this article and frankly, all of our blog posts and articles is to provide you the most thorough research and leading-edge thinking on subjects. For this post, we want to help you prepare for what may be coming in 2020.
Will We See Jail Time for Executives Under New Data Breach Legislation?
The infamous Equifax data breach started the conversation among politicians and some law enforcement that executives who managed organizations that are breached because of negligence on their part should be jailed. In an op-ed in The Washington Post last year, US Presidential candidate Elizabeth Warren suggests criminal penalties for leaders whose companies let data slip into the open.

In the article, Warren suggested, “My proposal would impose similar criminal liability for negligent executives of any company with more than $1 billion in annual revenue in a variety of circumstances, including if that company is found guilty of a crime or is found liable for a civil violation affecting the health, safety, finances or personal data of 1 percent of the U.S. population or 1 percent of the population of any state.”
She was backed up by Sen. Ron Wyden several months later whose proposal named “The Mind Your Own Business Act,” which suggested corporations could be fined up to 4 percent of annual revenue on their first offense. Company executives could face 10 to 20-year criminal penalties if they knowingly lied to the FTC.
The number of reported data breaches in Canada increased by six times after the country implemented a new breach-reporting regulation last year. The Personal Information Protection and Electronic Documents Act (PIPEDA) mandated that Canadian companies are required to report all the details of data breaches that occurred within the organization. They also need to notify affected individuals and keep records of all data breaches.
Cybersecurity experts have opined the Canadian government isn’t doing enough to protect businesses and consumers from data breaches and the public agrees with many suggesting that jail time may be the only disincentive that will work in the long run.
Will Ransomware Attacks Increase and Cost Organizations More?
Ransomware will continue to be the top attack tactic in cyber-crime according to Dr. Srinivas Mukkamala, CEO of RiskSense. He suggests “the reason is simple, it’s the shortest distance between investment and revenue for its perpetrators. Unlike, identity theft, crypto-currency theft, or bank fraud, ransomware is a fast, cheap, and effective method of extracting fees from victims.” Based on data from most cybercrime research organizations not only will the number of ransomware attacks increase, but also transition from targeting individuals to larger organizations.
To that point, Dr. Mukkamala further suggests that “the average ransomware demands have increased rapidly to $36,000 in the first half of last year.” But this number really understates the risk as perpetrators have adopted a more sophisticated pricing model which charges larger organizations much higher ransoms to unlock their data. Rivera Beach, FL, for example, had to pay $600,000 to unlock the city records encrypted by a ransomware gang while Korean hosting company Nayana paid $1m to unlock 3,400 hosted websites.
It is clear that cyber criminals across the globe have seen the level of damage they can inflict and the massive ransom payments some victims will pay to recover their data and systems. Last year, multiple U.S. organizations reported ransomware payments ranging from hundreds of thousands to nearly half a million dollars for payments made to cybercriminals.
Will SMB Threats and Attacks Continue to Rise?
In all likelihood, attackers will look to increase their development of exploits that take advantage of the well-known and publicized vulnerability in Microsoft’s Server Message Block (SMB) protocol. Ransomware such as Ryuk allows an attack on a single infected device to quickly spread from system to system and ultimately throughout an organization. Ryuk was derived from the Hermes source code and has been under steady development since its release 18 or so months ago. Ryuk has netted its operator “WIZARD SPIDER” $3,701,893.98 USD and because of the success of the malware for the criminal organization, the family of exploits used in the majority of ransomware attacks over the past several years will continue to devastate the millions of still unpatched endpoints; unfortunately, most are in SMB organizations.
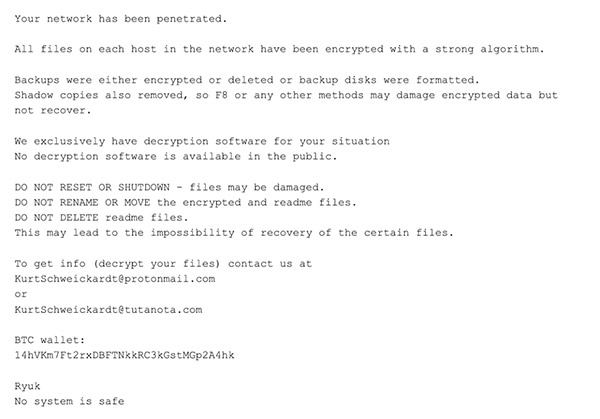
Ryuk Ransomware Note
Most ransomware attacks are largely targeting machines belonging to SMB’s in the US, which accounted for 53 percent of ransomware detections with Canada second at 10 percent. In addition, as we suggested in the previous prediction the average ransom payment increased by 184 percent to $36,295, as compared to $12,762 last year. Many of the attacks targeting businesses involve delivering the ransomware by exploiting unprotected Windows systems with the Remote Desktop Protocol (RDP) activated. Hackers, of course also like to use phishing emails that try to trick the victim into installing the ransomware.
It is interesting that 97% of United States’ companies refused to pay a ransom while only 25% of Canadian companies refused, followed by, 78% of German businesses, and 42% in the UK. On average, only 33% of companies that pay the ransom globally have their data unlocked or otherwise restored by the criminals.
Will Compliance and Privacy Take Center Stage in North America in 2020?
This one is almost a no-brainer as we have seen GDPR and CCPA go into effect over the past 18 months and demand significant compliance from organizations including putting the power of consumer’s PII back in the consumer’s control. In addition, privacy laws will result in an increased focus on employee accountability.
Countries like the US and Canada are following the European Union’s lead by implementing data protection laws like GDPR, such as CCPA which went into effect on January 1, 2020. They are also modeling privacy laws after legislation like the Thailand Personal Data Protection Act (PDPA) which goes into effect in May 2020. Under this legislation, the role of Data Protection Officers (DPOs) assumes significance as they must work closely with the CIOs and tech teams to ensure that organizations comply with the law. While the CCPA discusses the role of the DPO in organizations, at this point there doesn’t seem to be a mandate.
That said, with increased awareness of and emphasis on data protection, there will be an even greater focus on the handling of users’ personal data and its security. Employees at all levels will be held accountable as organizations strive to meet compliance. Privacy, compliance, and security are being asked to work together to protect their consumers, employee’s and prospect’s data. This is brutally difficult as understanding where the data lies in the organization, how it is being used, how it is being protected and most difficult, how to deal with the consumer’s various requests about their data will demand an increasing amount of time from IT security teams and likely take their focus off they enemy periodically.
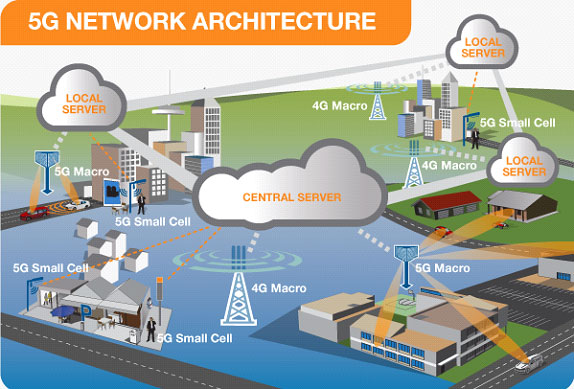
Will 5G Increase Cybercrime?
The fundamental idea behind 5G is a single network that is fast enough and flexible enough to handle a variety of different use cases. It is very likely that the introduction of 5G will result in the first public disclosure of a data breach caused by a mobile device. Lightning-fast 5G connectivity will enable new capabilities for remote robotic surgeries, autonomous cars, IoT in smart city infrastructure and traffic management and many other applications that require decisions to be made in milliseconds.
However, with those benefits, it will also add risks including the acceleration of the amount of data loss on mobile devices. 5G will continue to dissolve traditional enterprise network perimeters and cybercriminals will take advantage of security gaps to launch all kinds of attacks, such as phishing, man-in-the-middle, device takeovers, and more.
The bottom line is more devices and more software will result in more vulnerabilities for cybercriminals to attack. Distributing networks, virtualizing network functions, and millions or billions of smart devices will increase risks.
Happy New Year Again!
These were our top 5 IT security predictions including two that dealt more with compliance and privacy than they did with the nuts and bolts of cybersecurity. However, that is where we find ourselves with all the new compliance and privacy legislation coming from world governments.
We hope you enjoyed the blog post, please add comments to the posts so that we can provide the information you need or find interesting.
Have a Happy New Year and a Fantastic 2020!