Executing DSAR’s Under CCPA & GDPR
Better Solutions to Handling DSAR’s Under CCPA & GDPR
We’ve written about privacy, GDPR, and CCPA several times in this blog in order to clarify the requirements of current compliance legislation as well as new legislation that may impact organizations. As a matter of fact, this is our fourth “privacy compliance” post and one that we will use to try and make as comprehensive as possible since CCPA and GDPR are both current or “live” pieces of legislation which organizations will need to be compliant with as soon as possible.
Blog – Are Organizations Ready for The California Consumer Privacy Act (CCPA)?
https://secureops.com/privacy/blog-not-ready-for-ccpa/
Blog – How the California Consumer Privacy Act (CCPA) Will Impact Business
https://secureops.com/security/blog-ccpa/
Blog – Four Data Protection and Privacy Laws You Must Know
https://secureops.com/privacy/data-privacy-legislation/
Service – CCPA Guidelines and Requirements
https://secureops.com/solutions-portfolio/ccpa/
Ignoring CCPA and GDPR DSAR’s Will Cost Organizations in Fines
The CCPA is following in GDPR’s footsteps when it comes to levying fines for not following the stringent guidelines of the law. For example, the California Civil Code that defines one major sanction reads “civil class action lawsuits to pay statutory damages between $100 to $750 per California resident and incident, or actual damages, whichever is greater.”
This presents a much bigger issue for most organizations, as there is no limit on the number of private civil actions that might be launched, and the costs will be significant. The Equifax breach affected roughly 15 million Californians, meaning that if there were a similar breach to happen under the CCPA, they could have been liable for over $11 billion in claims, simply on the grounds of the consumer distress caused.
The CCPA isn’t just a state law — it will become the de-facto national standard for the foreseeable future because the sheer numbers of Californians, most businesses in the United States will have to comply.
While we’ve discussed the content of the legislation, we haven’t discussed the most challenging part of preparing and executing the requirements of the legislation for most organizations…DSAR’s.
What is a Data Subject Access Request or DSAR?
The term DSAR first gained popularity with GDPR but has accelerated significantly with the introduction of CCPA. DSAR stands for Data Subject Access Rights, however, what it has come to mean for organizations around the world is Data Subject Access Requests. CCPA, GDPR and other regulations give individuals the right to request information about the way companies handle their personal information.
Data Subject Access Rights are the rights provided to the consumer by the legislation while a SAR is the actual consumer request for information or deletion. In addition, you will see DSR, SAR, SRR, and VCR’s used interchangeably within organizations and even legal entities.
- DSR – Data Subject Request – identical to a DSAR
- SAR – Subject Action Request – identical to a DSAR
- SRR – Subject Rights Request – identical to a DSAR
- VCR – Verifiable Consumer Request – while this is like a DSAR, SRR, SAR, and DSR some organizations are interpreting this as the first step in completing a DSAR. Meaning, VCR is verifying the request that you received is from an actual data source in the system and not simply SPAM.
Regulations like CCPA gives individuals the right to request information about the way companies handle their personal information. A data subject makes his request via email, an online form, or another form of communication dictated by the guidelines of the law and the choice of the company. The company then needs to verify the requestor’s identity and existence within their database and track the request through to resolution. This process is required to be completed within 45 days to follow the compliance guidelines of CCPA – some exceptions allow up to 90 days.
Data Subject Access Requests are Costing Companies Millions
While the legislators in California who created GDPR & CCPA may have thought complying with the legislation would be straightforward for organizations, they may have underestimated the labor hours and cost of the legislation to companies. Considering all the moving parts for correctly operationalizing a DSAR, organizations have struggled to implement a viable solution.
Analyst firm Gartner predicts that, by 2021, 80% of the negative financial impact of the CCPA will spiral from a failure to implement scalable processes to manage these requests unless organizations find a way to streamline the way they respond to DSAR’s.
Let’s go through a simple bank transaction to understand the complexity of finding PII and matching it to the data subject.
Consider the following transaction:
- A single bank transaction may get replicated across 100 systems or databases within a large bank.
- Storage has become so inexpensive that enterprises have collected petabytes of data each year and have retained almost all of it in disparate databases.
- Data is routinely propagated across the organizations to provide access to a wide variety of users for various business initiatives.
As we have found with many data governance exercises within organizations, the massive growth in data collection and proliferation has not been accompanied by an equally matched effort in data management and data governance. In other words, organizations don’t know where all the personal information (PII) of their clients and customers resides in the systems, who in the organization has or has access to the data and worst of all, how to query the systems and databases to find it.
Because of the privacy legislation, companies are pouring resources into scouring systems to locate the data and organize it so that they can respond to DSAR’s. Significantly, this exercise will allow companies to better protect the data from hackers…who started this whole privacy and compliance ball rolling by breaching organizations and stealing billions of customer records.
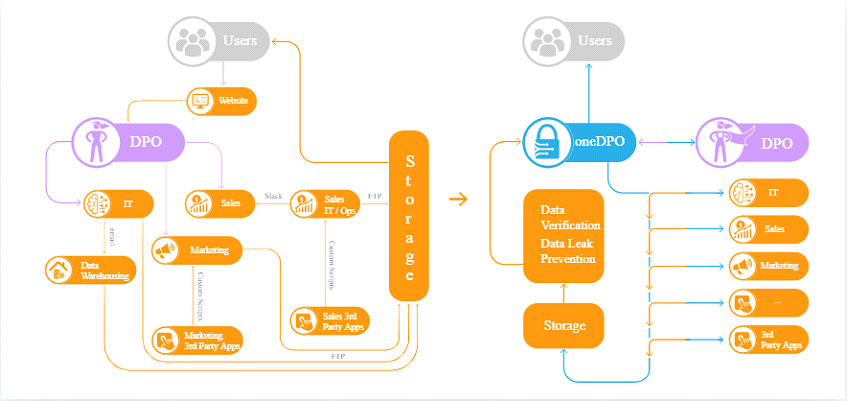
In addition, because of the massive increase in cyber-attacks over the past several years, many organizations were in the process of implementing security controls to block or restrict access to their data. However, whereas security is focused on who is using the data; privacy and CCPA are about how the data is being used and for what purpose. Until now, the basic data inventory or data governance process for many companies has been a manual one consisting of application data owner surveys and spreadsheets. IT Executives across the globe and particularly in the US are overwhelmed with the two projects.
What are the DSAR Requirements for CCPA Compliance
The California Attorney General’s office published fairly specific regulations that provide guidance on complying with Data Subject Access Requests (DSARs). Thus, we’ll take a look at the data a company must not only assemble, but also match to a data subject and make sure no other data from that data subject exists in the organization in case the data subject demands deletion. CCPA allows consumers the right to know what personal information:
- An organization has collected
- The categories of PII that have been collected (Birth Date, Social Security Number, Gender, etc.)
- Purpose of collecting the data
- With whom the data was shared with the outside of the organization
- Request deletion of their data
- Request the right to opt-out of the sale of their data.
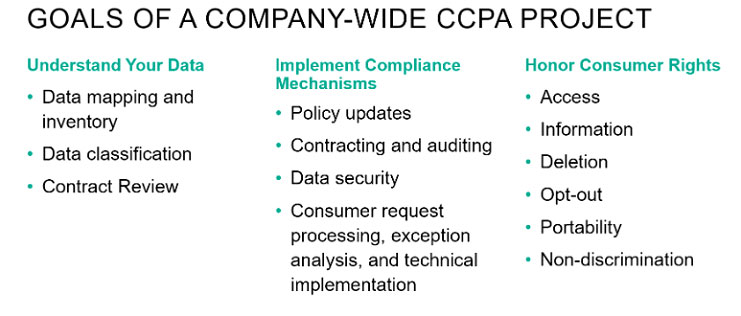
The regulations require that an organization offers two methods for consumers to submit those requests; one of those must reflect how the business primarily interacts with consumers (an online portal, a paper form, or a toll-free number, for example). Basically, the law was designed to make it easy for consumers to request their data and certainly not for the organization to comply with requests.
Managing and Responding to DSARs
Organizations would be wise not to cut corners when it comes to complying with SAR requests. According to the ICO’s own official statistics, the mishandling of SARs is the number one data protection issue the public is passionate about. In 2016, 42% of the 18,000+ data protection-related complaints lodged with the ICO concerned individuals’ rights to access their personal data held by organizations.
Any organization will need to have the following 6 capabilities to complying with DSAR’s accurately, cost-effectively and at scale:
- Submittal Form Requests: Request forms should enable consumers to select from a series of well-defined choices to help determine who they are and what their request is. This makes it much easier to respond, route, and manage requests versus having general or vague requests
- Automated Authentication: Organizations that have an established online account with their consumers can authenticate the requestor using PII that is already maintained by the business.
- Automate Search & Collection of Data: This will be the most time-consuming aspect of complying with CCPA for organizations that don’t invest in an intelligent, automated solution. Manual search involves finding the owners of the data in the organizations and then assembling the data manually from disparate databases or systems.
- Deletion: Organizations will be responsible to not only execute PII deletion requests from consumers, but also to verify across systems that none of the consumer’s PII has been inadvertently retained; and to confirm as such with the consumer.
- Align PII Retention Requirements with Legal Issues: Legal hold requirements may impact a customer’s request to delete their data in some cases. Organizations are often required to retain purchase records which contain customer PII.
- Document & Maintain an Audit Log of All Steps & Timelines: This is both a requirement of CCPA and from a legal standpoint, the most effective way of verifying compliance.
These 6 requirements clearly illustrate the need for an automated process and solution that handles the DSAR process from beginning to end. In addition, the solution needs to perform the hard work of scouring multiple and disparate systems for PII across the globe instantly and automatically. Further, the solution must:
- Document the relationship between data and consumer
- Assign owners of the PII and assets the DSAR submission
- Operationalize and maintain the process securely as mishandling of the data or failure to redact certain PII will undoubtedly result in fines or legal action
DSAR Requests will Cost Organizations Who Respond with Manual Processes
DSARs push the traditional manual process to its breaking point. Not only in people resources required to manually search those 100 systems in the bank example for each DSAR but also in the accuracy and completeness required to be defensible with the regulators. It is a big data problem and a new approach is required to process petabytes of data, extract key data points and derive the relationships between them.
Both GDPR and CCPA significantly increase the requirements on businesses regarding how they address individual rights and related requests (e.g., to access or delete personal information) – specifically the type of requests they need to address and the timeline and process they need to follow to fulfill the requests. For example, GDPR requires that requests be addressed within one month, CCPA within 45 days (with some exceptions and extensions permitted).
Automating DSAR Processes will Reduce Costs both in Labor Hours and Fines
Until now the organizations have been using data governance, data classification-based security, eDiscovery and even digital forensic tools to find and manage PII. These products are designed to find keywords or PII in files, email, and databases relying on pattern magic, using Regular Expression, GREP or other search functionality.
For use cases in compliance legislation like PCI or HIPAA where exact search criterion was available with only a limited volume of data and a small number of machines to scan, they solved the problem – sort of. However, the tools are too slow, complicated and inefficient to handle privacy use cases like DSAR. Because eDiscovery and data classification tools are not geared to search dozens of systems for specific information like PII they are generally not reliable at collecting personal information accurately and further have little ability to correlate the data to an individual.
The Steps to Automating DSAR’s Under CCPA & GDPR
CCPA will add risk, costs, and inefficiencies to organizations that do not implement an automated, intelligent solution. According to Gartner, manually fulfilling DSAR’s is estimated to cost $1,400 per each request. Further, according to a separate Gartner survey which was cited in its white paper “How to Prepare for the CCPA,” 83% of respondents “needed a full working week or more time to respond to every single request.”
Consider what happened to Microsoft when it opened its DSAR portal in compliance with the EU’s General Data Protection Regulation (GDPR). In the first year, it received 18 million data requests. Over 6.7 million came from US consumers.
The key to minimizing costs, maximizing efficiency and eliminating risk is implementing a solution that will:
- Automate DSAR Management
- Secure Fulfillment of DSAR’s
- Continuous Monitoring and Tracking of Requests
- Automate PI Data Linking
- Monitor and Track Customer Consent
- Assess CCPA readiness
- Assess 3rd Party Compliance
- Map PII Data Flow
We’re SecureOps and we do not endorse any one of the numerous types of “intelligent” software that leverages AI and machine learning to identify PII across an organization. Further many of these types of software help manage the process of taking in DSAR’s and tracking them through the system. That said, we work with organizations to implement holistic, cost-effective solutions that leverage the best of breed technology that will suit our customers for the long term.