How Companies Use CIS 20 to Secure Remote Workers
Using CIS Controls 1-6 to Secure Your Remote Employees
As we in the industry have documented consistently, Cyber-attacks continue to grow in sophistication and damage particularly over the past several months. For example, we previously wrote about the Industrial Control System (‘ICS’) Ransomware which targets ICS applications through enhanced encryption features including ‘kill’ applications and clever obfuscation techniques. We have also written about how attackers are exploiting the COVID-19 or Coronavirus pandemic and specifically about their attacks in two previous blog posts.
While we touch on how attacks against remote employees could escalate into the corporate systems, CIS, or the Center for Internet Security, has provided several stern warnings to organizations and produced an excellent guide called CIS Controls and Small Office Network Security Guide for upgrading the security of your remote workers. The guide does a fantastic job of going through a remote office set up step by step in the 28-page document including mapping CIS controls to remote office security, however, we are going to try and provide some simplicity around the 6 CIS controls that will improve remote employee security significantly.
Thus, in this article, we set out how CIS 20 provides six basic controls that are a useful start for your information security strategy.
CIS 20 Provides a Framework to Improve Overall IT Security
As we touch on in the opening paragraph, ‘CIS 20’ is the name given to “The Center for Internet Security Critical Security Controls for Effective Cyber Defense.” It provides a set of controls or standards which has become a ‘best practice’ guide for information security controls.
CIS 20 is not law, and it is not usually a compliance requirement. In this sense, it is not like the Payment Card Data Security Standard (PCI DSS), which is a compulsory information security standard for branded credit cards or HIPAA for health care organizations or even Sarbanes-Oxley or SOX for financial institutions.
CIS 20 also stands in contrast to ISO/IEC 27001 Information Security Management. This standard also provides a set of controls for developing an information security strategy. However, ISO 27001 is a more complex (114 controls, rather than 20) standard, is part of a larger security framework and relies on each organization carrying out its own risk assessments. In light of this, it is a less ‘user-friendly’ set of guidance than CIS 20.
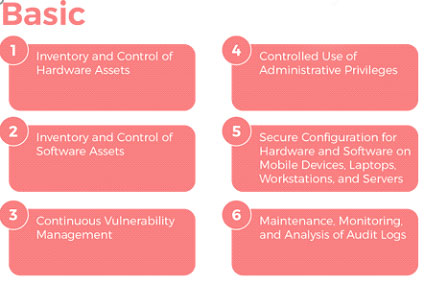
Helpfully, CIS 20 is divided into three prioritization categories: basic, foundational, and organizational. In this article we only look at the ‘basic’ controls; the first six controls that every organization should have in place for its remote workforce.
Implementing the First Six ‘Basic’ CIS Controls Quickly & Effectively
The six basic controls are a ‘bare minimum’ for protecting your organization from cybersecurity risks. But implementing CIS 20 doesn’t just make good business sense – an additional advantage is that it goes a long way towards satisfying the legal requirements of the General Data Protection Regulation (GDPR), California Consumer Protection Act (CCPA) and other data protection laws, which require that robust systems be in place for the protection of customer personal data.
Below we examine each of the six basic CIS 20 controls in sequence and describe how they can be used to enhance the cybersecurity of your organization.
CIS Control #1: Keep an Inventory of Hardware Assets
Even in the normal working environment, it is common for staff to use unauthorized devices, such as their personal smartphones and devices, to access workplace systems. Now, with workers primarily based in their own homes, this practice has increased dramatically.
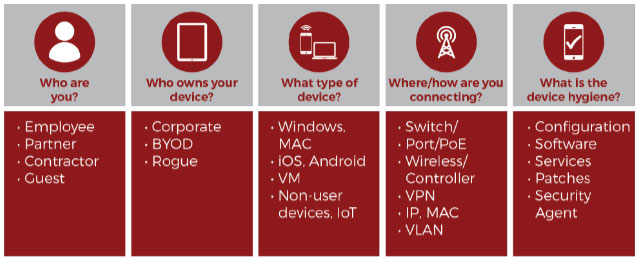
This control means that you need to keep track of all devices, whether they have been authorized to have access to the organization’s assets, or not. To comply with this control, it is recommended that organizations implement an automated inventory tool that keeps track of all devices connected to organization networks.
Pay particular attention to any new equipment issued to staff (such as laptops issued ahead of the lockdown): All equipment acquisitions should have resulted in an automatic update to the inventory.
Inventory listings should include:
- the type of device
- whether it is portable
- whether it is a personal or corporate device

CIS Control #2: Keep an Inventory of all Software
We all have our favorite apps for things like email, messaging and note-taking, however, employees should not simply be using whichever software they prefer while handling employer work. With so many employees working from their own homes, there may not be the same level of natural oversight to ensure that employees are only using organization-sanctioned software.
The use of non-sanctioned software presents a significant security risk due to software vulnerabilities and other flaws that may be a security gap in the software. In addition, the organization has a legal responsibility to protect customer personal data which means ensuring that any organizational software will protect that information.
As its control, the organization should have an authorized set of software and versions that are permitted in the organization. This software should be continuously monitored to ensure that it has not been modified. Organizations might also consider ‘Whitelisting’ technology which can be used to ensure that only authorized software can run, or the use of virtual machines for higher risk business operations.
CIS Control #3: Continuous Vulnerability Management
In tandem with CIS Control #2, Control #3 deals with managing and fixing vulnerabilities that inevitably expose organizations to attacks. The way in which cyber-attacks, such as malware, ransomware, and phishing attacks continue to increase relies on the increasing amount of software used and the corresponding number of vulnerabilities that are discovered.
Thus, there must be a comprehensive program in place for identifying and managing any vulnerabilities before they are exploited by attackers: ‘Vulnerability management’ needs to be a continuous project.
As well as having a vulnerability scanning tool in place to identify these vulnerabilities, you also need to make sure automated security updates are in place to continuously update software for new threats.
CIS Control #4: Controlled Use of Administrative Privileges
Administrative privileges are the set of abilities certain users are provided to make major changes to a system or even simply access systems. In the COVID-19 working environment, there may be a temptation to hand out administrative privileges rather liberally. Administrators are stretched trying to get dozens, if not hundreds of workers set up and productive in their new work environment and security has become a lower priority.
However, administrative privileges constitute a major potential vulnerability of an organization, so they need to be carefully managed. If a cybercriminal manages to get a privileged user to download malware the power of administrative accounts means the attacker can escalate credentials to do untold damage.
To guard against this threat, organizations must keep a tight rein on administrative accounts, providing access to staff only when necessary. Staff should be reminded that those with administrative privileges should only log in to their administrator account as and when required. They should not be logged in while working on other activities.
CIS Control #5: Secure Configuration for Hardware and Software on Mobile Devices, Laptops, Workstations, and Servers
The ‘factory pre-set’ for operating systems and applications is usually optimized for ease-of-use rather than security. The organization needs to ensure that any default configurations are replaced by security configurations appropriate to the risks faced by the organization. Basic configurations such as open ports might be exploitable under default settings.
Furthermore, once secure configurations are in place, they must be continuously updated to account for the continuous stream of security threats that an organization faces.
As part of a secure configuration, a monitoring system should be in place. This will check the configuration settings and keep track of any exceptions and alert when unauthorized changes occur.
CIS Control #6: Maintenance, Monitoring, and Analysis of Audit Logs
You cannot protect your organization from what you do not know about. All attacks and threats need to be logged in order to allow for an investigation. This is the purpose of an “audit log.”
However, this audit log can’t simply be treated as a compliance exercise – criminals rely on the tendency of organizations not to check these logs; meaning that threats can go undetected for a long time.
With the proliferation of devices in the remote work environment, it is crucial to have software in place that sends all threat log information to a centralized audit log which is continuously monitored.
Conclusion
Dealing with the threat of cyber-attack to your organization might feel overwhelming, however, the CIS 6 for our purposes will provide a useable framework for most organizations. The basic controls in the CIS 20 are a set of clear, actionable steps that all organizations can take to implement a cybersecurity strategy. Clearly, CIS 6 isn’t designed to stop all threats, however, in the 80/20 world, they are an exceptionally good start to improved security.
To Learn More About How to Protect Your Organization through a Cybersecurity Strategy Please Call Us – as Always We Are Happy to Help – 1 (888) 982-0678







