The Fundamental Elements of Cyber Hygiene
Cyber Hygiene or IT hygiene involves best practices related to cybersecurity to protect your network and infrastructure from threats. It serves as the basic foundation for a proactive, systematic, and comprehensive approach to data protection. Taking the time to create cyber hygiene priorities ensures you’re not providing a malicious attacker with the opportunity to take advantage of gaps and vulnerabilities in your network.
However, strengthening an organization’s cyber security hygiene is complex; and dealing with the challenge of technology, as many organizations do, isn’t enough. The process should start with implementing fundamental cyber security practices, which we believe are the foundation of Cyber hygiene. Just like personal hygiene, Cyber hygiene’s objective is to start with basic actions that are most likely to support good health. Despite the popular belief that cyber hygiene is exclusively the IT department’s job; however, Cyber hygiene should involve all departments and be part of the organization’s culture.
Cyber hygiene is a broad, critical topic for IT security and frankly, it often has different definitions with top IT security consulting firms. In addition, their perspective of achieving good Cyber hygiene is different and can be somewhat nebulous and complex as well.
The goal of this blog post is to provide you with a clear definition of Cyber hygiene and what we at SecureOps believe are the fundamental elements to achieving a quality Cyber hygiene program. I’m absolutely certain that experts all over the cybersecurity community could argue what elements are most critical to improving an organization’s overall security posture and Cyber hygiene. That said, we’ve put our heads together here at SecureOps to introduce the fundamentals that we believe are key.
In many ways Cyber hygiene is synonymous with an organization’s security posture; I hope we can agree on that. I’m suggesting that if an organization has a good security posture and scores well across a NIST, ISO, or CIS 20 framework, their Cyber hygiene will be excellent as well.
Implementing a Trusted Cybersecurity Framework
Cybersecurity frameworks provide a blueprint for identifying, prioritizing, and creating an ongoing plan for organizations to improve their posture over time with audits and scoring. Let’s start with the CIS 20; it is by far the easiest to understand, use and score with far few items to assess than both the NIST and ISO assessments.
The Center for Internet Security (CIS) Top 20 Critical Security Controls (previously known as the SANS Top 20 Critical Security Controls), is a prioritized set of best practices created to stop the most pervasive and dangerous threats of today. It was developed by leading security experts from around the world and is refined and validated every year. One of the keys here is addressing the threats of today.
CIS developed a set of gold standard guidelines for organizations facing data security issues- the Critical Security Controls to simplify and help IT operations and security teams remain focused on the essentials. These activities ensure that the CIS Controls are not just another list of good things to do, but also a prioritized, highly focused set of actions with a community support network to make them implementable, usable, scalable, and compliant with all industry or government security requirements. CIS controls defense strategy is based on three key points:
- Reducing the attack surface by hardening the device configuration.
- Identifying vulnerable machines to alert long-term threats in the organization’s network.
- Distributing the attackers and establishing defense and response capabilities.
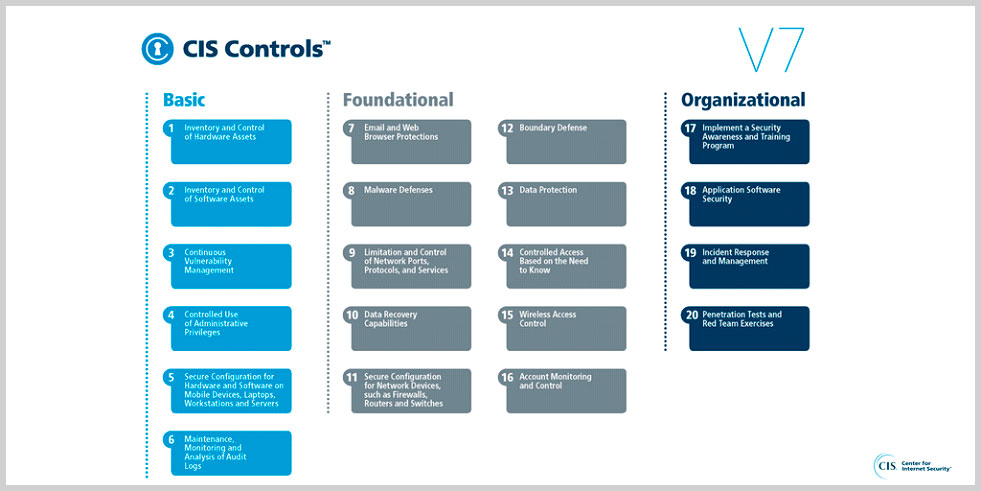
Figure – You can find this image here – https://twitter.com/cisecurity/status/989854211281211393?lang=de
A study of the previous CIS Controls found that 85% of cyber incidents could be prevented by implementing only the first five controls.
Getting started with any one of the frameworks is fairly straightforward. All of the frameworks essentially start by asking yourself these questions to assess how well the organization is managing cyber risk:
- Do you know what is connected to your computers and networks?
- Do you know what software is running on your systems and networks?
- Do you set up your computers with security in mind?
- Do you manage who has access to sensitive information or who has extra privileges?
- Is your staff clear about their role in protecting your organization from cyber incidents?
Vulnerability Management Best Practices are Critical
Vulnerability management exists for the purpose of identifying and remediating vulnerabilities in systems quickly before they are exploited. Vulnerabilities are essentially weaknesses within the software that can lead to a system or network that can be exploited by attackers. These vulnerabilities must be identified, assessed, and patched regularly to ensure ongoing security. The old process of patching on a regular schedule, every week, month, or more will leave organizations exposed. Read our blog post on Log4j/Log4Shell to see how cybercriminals scanned systems globally to find vulnerable systems – https://secureops.com/blog/log4j-a-case-study/.
In order to create and maintain a quality security posture, security must be keenly aware of the vulnerabilities on their systems, as well as the process by which they can be quickly patched. If vulnerabilities are not identified or remediated, companies leave themselves open to attacks.
According to a recent Verizon’s Data Breach Investigation Report, “98% of security incidents and 88% of data breaches continue to occur within one of nine patterns.” Understanding and taking steps to guard against the common patterns and approaches attackers use to infect your system will greatly increase the security posture of your company. The most important way to do this is to frequently scan for known vulnerabilities. These common weaknesses often have patches available from the software manufacturer that will eliminate the vulnerability.
Developing Incident Response Capabilities
Almost a third of US businesses were breached last year according to an HSB survey of 403 senior executives in the U.S., conducted by Zogby Analytics. HSB, a leading provider of cyber insurance for businesses and consumers suggested that with an increasing amount of both personal and business data available online, the risk of exposure will increase in proportion. The financial impact of a data breach reported in the survey was considerable as well: 27 percent of the victim organizations spent between $5,000 and $50,000 to respond to the breach and 30 percent spent between $50,000 and $100,000.
The survey also revealed that 51% of the executives thought their IT security staff “lacked a plan” to deal with the breach, 41% didn’t have the required knowledge to handle the breach adequately and 38% lacked the resources.
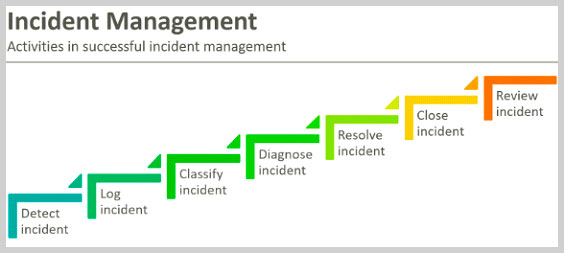
Figure – In ITIL, incidents go through a structured workflow
Ponemon Institute shocked the cybersecurity industry a number of years ago when they published a survey of 567 executives, of whom 43% suggested they had experienced a data breach or perhaps a security incident, if you examine the details in the survey, in the prior 12 months. While security incidents and data breaches are apples and oranges, the trend and any back of the napkin analysis paints a fairly grim picture – the number of organizations that are damaged significantly from a cyber-attack is growing at a rapid pace.
The Ponemon survey also revealed that 68% of respondents felt unprepared to respond to a data breach and 30% of respondents felt their data breach response plan was flat-out ineffective. Clearly, the response to security incidents has not improved in proportion to the sophistication of the attacks as well as the number of attacks.
Why Good Cyber Hygiene is so Critical to Protecting Organizations from Attacks
In a recent Forrester Consulting survey, 94% of security and business executives found that their organizations have experienced a “business-impacting” cyberattack or compromise in the past year. Business-impacting according to the survey is defined as an attack that resulted in the loss of customers, employees, or confidential data (PII). Further, any interruption of day-to-day operations, a ransomware payout, or other financial loss or theft of intellectual property would be included.
That’s a very powerful number, especially when talking to the executives in the C-suite,” says Forrester analyst Wenzler. “Security pros can now go to top management and offer proof that cyberattacks will impact their businesses and that they have to do something about it.”
Meanwhile, threats go beyond technology and external hackers. Human fallibility is often the root cause of breaches. Cyber-attackers are no longer breaking in—they’re logging in using weak, default, or compromised passwords. Once they compromise security measures, adversaries are able to inflict real damage by moving laterally across the network, seeking privileged access to critical infrastructure and sensitive, potentially valuable data.
The IT department alone cannot mitigate identity-based attacks. Ultimately, it’s a responsibility shared by all employees from C-suite to summer interns, as well as partners and contractors. “If you look at the most major ransomware attacks that have occurred, basic cyber hygiene could have prevented the vast majority of them, so, killing their ability to move laterally,” Matthew Swenson, chief of the Department of Homeland Security’s (DHS) Cyber Crime Unit at Homeland Security Investigations (HSI), said during a recent webinar. “Heavy network segmentation, network security monitoring, zero-trust models, multi-factor authentication, all those types of things.”
“I think you start from the basic cyber hygiene, work your way up, and as you start to prevent just those basic things and get more and more secure, I think you do end up preventing the vast majority of these types of attacks,” he added.
Conclusion
Security vulnerabilities are weaknesses, whether they are in applications, systems, people, or processes that allow attackers to compromise a system and the information it is supposed to protect. Today, minimizing your attack surface and overall risk exposure requires a continuous approach that increases visibility over vulnerabilities and enables rapid remediation.
Many security leaders see Cyber hygiene as somewhat theoretical rather than something measurable that their organization should strive to identify and set goals to reduce. Most professionals in the IT security or cybersecurity industry understand it is difficult to set a value to systems, litigation costs, brand damage costs, ransomware payments, data loss costs, compliance penalties and so many other difficult to estimate variables.
Thus, Cyber hygiene best practices are often not implemented or measured because of their complexity, cost, intangible benefit, and lack of a standardized blueprint. However, having implemented Cyber hygiene best practices across some of the world’s largest and most complex organizations has allowed us to confidently suggest to our readers that a good vulnerability management program, a security posture assessment, and implementation of incident response processes are excellent places to start.







