Malware: Old Tools; New Tricks
Since the earliest form of a computer virus was created in 1949, malware has certainly come of age. Malware continues to wreak havoc on corporate and government entities and remains a perpetual thorn in the side of vendors and IT teams. But it’s not a gap you can simply plug and “be done with.” As we said in a previous blog post, The Evolution of Malware, “since the creation of the earliest form of computer viruses, the method, and intent of malware have evolved dramatically. Beginning with John Von Neumann’s “self-reproducing automata” in 1949, the understanding of how to create programs that can replicate and spread themselves across networks has opened doors to numerous new advances – both good and bad.”
We also discussed the Creeper Worm which was the next notable computer virus. “Developed in 1971 by Robert Thomas, the virus spread across the ARPANET to remote computers where it shared the message, “I’m the creeper, catch me if you can!” The ability to create such a program that could clone itself was a huge discovery.”
An Endless Game of Cat and Mouse
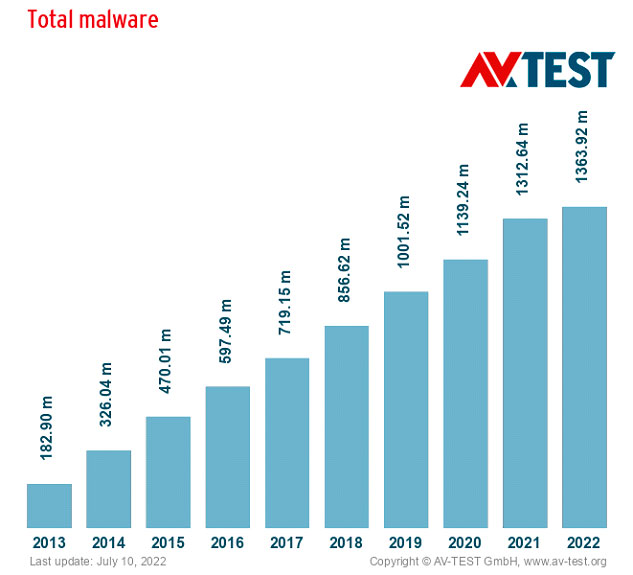
Malware variants continue to grow in scope and sophistication. Threat actors work quietly behind the scenes persistently and aggressively, adapting new techniques and strategies into their design paradigms. Every new platform that emerges represents another lucrative opportunity. The intrinsic cat and mouse game between malware developers and IT security that’s been going on for years shows no sign of stopping.
Malware developers and distributors are well-organized and well-funded, so they can invest time and energy into honing their craft. Moreover, as many operate from locations where there are few laws prohibiting such activity like Russia and China, they know the risk of negative consequences is low.
As a result, all too often, new flavors of malware emerge, decimate their victims, then disappear… only to raise their ugly heads once again after a few months or even years.
In this post, we’ll review some of the most persistent and perilous malware strains of recent years, understand their mechanics and targets, and consider some strategies you can adopt to raise your defenses against them.
Devil in a New Dress
The Cybersecurity & Infrastructure Security Agency, in partnership with the Australian Cyber Security Centre, recently issued a Cybersecurity Advisory detailing the top malware observed last year. It shines a light on the tenacity of cybercriminals and the adaptability and resilience of their malware.
According to the Advisory, the top malware detected in 2021 included remote access trojans, banking trojans, information stealers, and ransomware, which we discuss in depth in a previous blog post titled, Ransomware and Business Email Compromise (BEC) Account for 70% of Breaches. Specifically, these included Agent Tesla, AZORult, Formbook, Ursnif, LokiBot, MOUSEISLAND, NanoCore, Qakbot, Remcos, TrickBot, and GootLoader.
Their use cases and victims were varied. Threat actors used Qakbot and TrickBot to create botnets for use in ransomware attacks. Meanwhile, Formbook, Agent Tesla, and Remcos were instrumental in mass phishing campaigns that exploited COVID-19 themes to deliver ransomware or steal personal and financial information.
The Agencies also revealed that certain forms of detected malware were actually marketed as legitimate software. For example, the developers of Agent Tesla and Remcos have marketed the software as authentic tools for remote management and penetration testing.
They also highlighted that, in many cases, developers created malware and passed it on to malware distributors, who in turn brokered it to malware end-users.
Among the Cybersecurity & Infrastructure Security Agency’s comments of particular concern was that much of the malicious code detected has been systematically supported, improved, updated, and reused over several years, which contributes to its longevity.
In fact, most of 2021’s top malware strains have been used for more than five years – and some for more than 10 years – with their respective code bases evolving into several different variations.
Of these, Agent Tesla, AZORult, Formbook, LokiBot, NanoCore, Remcos, and TrickBot have been used in attacks for at least five years, while Qakbot and Ursnif have been used for more than a decade.
Know Your Enemy
Let’s take a look at the long and checkered history of some of the top malware performers of 2021 who made the headlines for all the wrong reasons:
Qakbot
Active since 2007, Qakbot has evolved from a general banking trojan in its capabilities and can now perform reconnaissance, move laterally, gather and exfiltrate data, and deliver payloads. As it’s modular in nature, it’s easy for cybercriminals to configure it to their needs.
Ursnif
Active since 2007, Ursnif is a banking trojan used to steal financial information. It’s evolved over the years and now includes a persistence mechanism and the ability to avoid sandboxes and virtual machines.
NanoCore
Active since 2013, NanoCore targets victims’ information such as passwords and emails and can also allow cybercriminals to activate PC webcams to spy on victims. Malware developers continue to introduce new capabilities and offer them for purchase on the Dark Web or as part of a malware kit.
Agent Tesla
Active since 2014, Agent Tesla steals data from web browsers, mail clients, and File Transfer Protocol (FTP) servers. It can even capture videos, screenshots, and clipboard data. Its developers continue to add new functionality, such as obfuscation capabilities and targeting of additional applications for credential theft.
AZORult
Active since 2016, AZORult is used to steal data from compromised systems. It’s sold on underground hacker forums as a tool for stealing browser and cryptocurrency information and user credentials. Its developers regularly update its capabilities.
TrickBot
Active since 2016, TrickBot is often used to form botnets or enable initial access for ransomware or banking trojans. It’s developed and operated by a highly sophisticated group of malicious threat actors who have evolved it into modular, multi-stage malware.
FormBook
Active since at least 2016, FormBook is a popular information stealer. Its capabilities include key logging and accessing browser or email client passwords. Its developers regularly update it to exploit the latest Common Vulnerabilities and Exposures (CVSs).
The Anatomy and Evolution of Malware
So, how exactly do malicious actors manage to morph and evolve their malware products so frequently and, seemingly, with such ease?
In the early days of cybercrime, malware developers typically adopted two tactics when plotting their malware attacks:
- Employing a variety of different tools, each for a different purpose
- Leveraging a single piece of malware with an extensive set of features
However, in recent years their strategies have become more agile and sophisticated. Rather than using many disparate tools and resources to build a monolithic, all-purpose application, they adopt a similar approach to what’s used in developing modern large-scale software. In this model, malware authors collaborate on a single platform with an advanced plugin interface.
These plugins make it easy for them to extend their malware’s functionality, for example, the ability to gather a user’s password or detect anti-malware applications or anti-sandbox, anti-debug, and anti-analysis techniques.
This more cohesive, modular approach hinders researchers’ ability to detect, analyze, and report on malware while giving attackers the flexibility to adapt their tools and deployment strategies to new situations and environments.
Malware Mitigation and Key Takeaways
As attackers continue their covert behavior and develop and unleash new iterations of their malware, it’s vital to stay vigilant. This means understanding how malicious software can be disguised and where the weak points in your systems might be.
At SecureOps, we emphasize the following actions to stay ahead of the malware threat:
- Develop a comprehensive risk management strategy and incident response plan, so you know exactly which systems and data need to be protected and what to do in the event of a breach.
- Regularly update your software, including operating systems, applications, and firmware.
- Prioritize patching for known exploited vulnerabilities.
- Implement network segmentation to separate different parts of your network based on their role and functionality. This will help prevent the spread of ransomware and thwart attackers’ ability to move laterally over your network.
- Invest in a robust offline backup solution to protect your sensitive company information from ransomware attacks or other potentially devastating incidents of data loss, corruption, compromise, or theft.
- Be sure to stay abreast of evolving malware threats so you can proactively improve your defense posture.
- Enforce multi-factor authentication and don’t allow passwords to be used for multiple accounts or stored in systems to which adversaries could gain access.
- Train your employees so they remain vigilant about phishing attacks and social engineering and spearphishing campaigns.
To learn more about how to protect yourself from malware attacks, please call us – as always, we’re here to help – 1 (888) 982-0678